There may be many fish in the sea, but there are even more in the digital ocean. That is, perhaps, why phishing is the favorite pastime of so many cybercriminals. The problem in this scenario is that they’re phishing for your data.
What is Phishing?
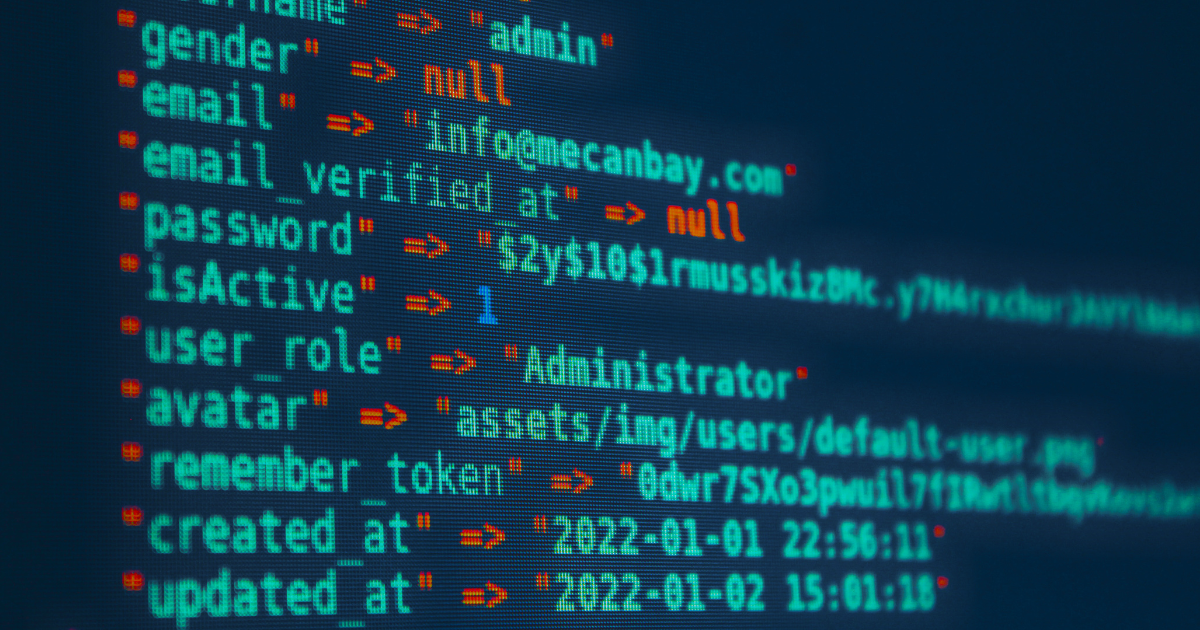
Phishing is a type of cyberattack where criminals try to steal your data. They send you an email pretending to be a legitimate service or entity. From there, you’re diverted to an external website and asked to provide certain information, such as your username and password.
The problem is that the website you’ve been diverted to isn’t legitimate. It will be a site that looks legitimate but belongs to cybercriminals. They can see any information you enter on this site and use it to access your account.
Five Modern Types of Phishing Attacks Every Malaysian Business Should Know
Phishing today goes far beyond shady emails. Cybercriminals have drastically evolved their tactics — using voice calls, AI-generated deepfakes, SMS, fake websites, and even live chat widgets to trick victims into handing over sensitive data or funds.
Here are the most common — and dangerous — forms of phishing Malaysian businesses face in 2025:
1. Email Phishing: Still a Threat, But Now AI-Powered
Email phishing remains widespread — but the game has changed. Today’s attackers use GenAI tools to craft grammatically flawless, highly persuasive messages that mimic legitimate organizations, including banks, telcos, and government bodies like LHDN or MySejahtera.
These emails often:
- Ask you to verify your account or reset your password
- Warn of “unauthorized login attempts”
- Link to CAPTCHA-protected phishing sites that appear secure
Real-life scenario
A user receives an urgent email from “Maybank,” complete with a CAPTCHA-protected link that leads to a lookalike Maybank2u login page. AI-generated content and HTTPS give it false legitimacy — making it easy to fall for.
2. Spear Phishing: Hyper-Personalized and Harder to Detect
Spear phishing uses publicly available info (e.g., LinkedIn, press releases) to craft tailored messages. With the help of AI, attackers mimic tone, formatting, and signature blocks, making the email feel authentic.
Often aimed at mid-level executives or finance teams, these emails are built for trust — and urgency.
Example: A finance manager receives an email appearing to be from the CEO, requesting an urgent payment for a vendor in Singapore. The language is formal, the logo is right, and the signature matches — but it’s a clone sent from a slightly altered domain.
3. Whaling: Top Executives Targeted with Deepfakes
Whaling targets senior leadership — CEOs, directors, CFOs — with highly convincing emails, voice calls, or even video messages.
In 2025, attackers now use deepfake voice and video impersonation to pose as trusted colleagues or partners during Zoom calls or voicemail requests.
Scenario: A Malaysian real estate CEO receives a voice note from someone sounding like their regional partner, asking for approval on a high-value fund transfer. It’s later discovered the voice was AI-generated using cloned audio samples from YouTube.
4. Smishing: From Fake Bank Apps to Courier Scams
SMS-based phishing (smishing) continues to surge in Malaysia, especially with scams involving:
- Fake banking apps (e.g., CIMB, RHB)
- Courier delivery updates (e.g., PosLaju, DHL)
- Government cash assistance programs (e.g., eMadani)
Attackers use short links and push urgency like “Your parcel is being returned” or “Tap here to claim your rebate.”
Local alert: Bank Negara and MCMC have repeatedly warned the public about malware-laced APKs sent via smishing — which can silently hijack credentials and intercept SMS OTPs once installed.
5. Business Email Compromise (BEC): Patience + Precision = Millions Lost
BEC attacks are among the most financially devastating forms of phishing. Unlike spray-and-pray methods, attackers:
- Gain access to real business accounts
- Lurk silently for weeks, watching conversations
- Strike when a payment or invoice is due
They inject small but costly edits — like a change in bank account number — into ongoing threads.
Real case: A logistics company in Johor unknowingly paid RM580,000 to a scammer when an attacker, having breached their vendor’s email, modified a legitimate invoice email just before payment.
Example of a Phishing Attack
You receive an email from Maybank telling you your account has been compromised. You’re asked to click a link and log into your Maybank account to reset your password. You duly follow the instructions.
Once you’re done, the criminal will have your username, old password, and the “new” password.
Notable Statistics and Phishing Incidents in Malaysia

Phishing emails today are getting incredibly sophisticated. They so closely mimic legitimate businesses that often, even experienced users can’t tell them apart. To better protect clients from dangerous emails, we are moving towards AI-assisted detection and blockage.
Bernard Tan
CallNet Senior Systems Engineer
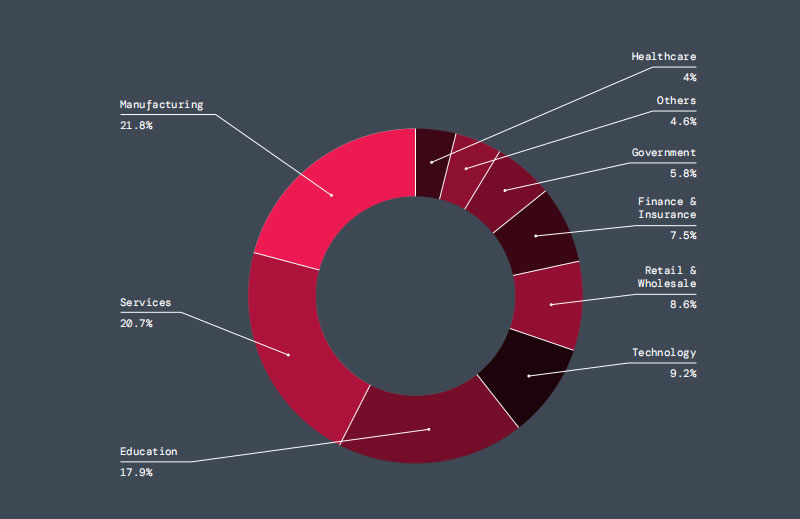
Across 2022, Southeast Asia experienced over 43 million phishing attacks. Of those, 8.2 million targeted Malaysians. While we love being at the top, ranking as the number two country targeted by phishing attacks isn’t something to celebrate.
Other phishing incidents in Malaysia include:
- In 2023, Cybersecurity Malaysia warned of a phishing site link being spread via Telegram. The site mimicked MyKasih Sumbangan Asas Rahmah (SARA).
- Hacker group Dark Pink tried to steal confidential military data. They used phishing attacks to target the emails of several Malaysian defense agencies.
- The Royal Malaysian Police arrested eight individuals in 2022 for providing Phishing-as-a-Service. The group had been active for years and even sold stolen credentials.
How to Protect Yourself From Phishing Attacks
Phishing emails are no longer easy to spot. Today’s attackers use AI to craft flawless, convincing messages, hijack legitimate accounts, and even use tools like CAPTCHA, voice calls, or deepfake videos to build trust and bypass traditional security checks.
Even worse: Some phishing pages now bypass 2FA by stealing session cookies — making MFA alone no longer enough.
Here’s how to defend yourself and your organization against the latest phishing threats:
- Always Be Skeptical — Even of Familiar Names Phishing is no longer limited to fake domains. Attackers often compromise legitimate accounts and continue email threads that seem trustworthy. If an email contains an unusual request, question it, even if the sender appears legitimate.
- Inspect the Email Address and Tone Look closely at both the sender’s address and how the message is written. AI-generated emails often appear flawless but may use overly formal or urgent language. Be alert to slight domain changes, odd sentence structures, and inconsistent branding or email signatures.
- Avoid Clicking on Links Without Verification Many phishing campaigns now use realistic-looking sites hidden behind CAPTCHA pages. Instead of clicking, hover over links to preview them. Type trusted URLs directly into your browser, and avoid using links sent via email or SMS unless you’re sure they’re safe.
- Use Advanced Security Tools Basic antivirus is no longer sufficient. Use security solutions that include real-time threat detection, SSL/TLS inspection, and browser isolation to analyze suspicious websites safely. Choose platforms that can detect and block newly registered phishing domains and AI-generated attacks.
- Enable MFA — But Don’t Rely on It Alone While MFA remains a vital defense, some phishing kits can intercept one-time codes and session cookies. Strengthen your security by enabling device-based authentication, session monitoring, and contextual access controls such as location or device fingerprinting.
- Verify Contact Details Through Official Sources Do not trust phone numbers or links found in unexpected emails. Instead, verify requests by contacting the person or company through a known phone number or website. This is especially important for financial, legal, or vendor-related communications.
- Monitor Your Accounts Regularly Check your financial and critical service accounts for unusual activity on a regular basis. Set up login alerts where available, and review your account history for changes to contact details or payment settings.
- Conduct Phishing Simulations and Staff Training For organizations, regular phishing simulations and security awareness training are essential. Modern phishing involves not just emails but also calls, text messages, and even fake video or voice communications. Equip your team to recognize and report these threats early.
phishing Protections for Small business & enterprises
The conclusion of a successful phishing expedition can be extremely painful for victims. Once they provide cybercriminals with the necessary data, they likely won’t know something is wrong until it’s too late.
To enhance your defense against phishing attacks, it’s crucial to consider solutions from renowned cybersecurity brands. Prominent brands like Cisco specialize in preventing phishing by using advanced detection techniques and offering robust security measures that can be integrated into your existing cybersecurity protection.
Be proactive, and you can run your business with peace of mind. Don’t wait until it’s too late. For more detailed strategies and tools against phishing attacks, talk to our cybersecurity expert at Callnet Solution.