Cloud security protects business data stored and processed in the cloud. For Malaysian companies, the move to platforms such as AWS, Microsoft Azure, and Alibaba Cloud has brought faster scalability and better collaboration.
However, cloud platform introduces new risks: Data breaches, ransomware, and regulatory non-compliance can disrupt operations and damage customer trust.
By applying proven best cloud security practices, you can strengthen their defenses while keeping day-to-day operations smooth. This article explains eight practical cloud security measures and why they matter for enterprises in Malaysia.
What is Cloud Security and Why Does It Matter for Businesses?
Cloud security is the set of technologies and policies that protect, monitor, and prevent threats targeting cloud-based systems. It covers areas such as data encryption, access control, firewalls, backups, and compliance monitoring.
For businesses, the stakes are high. A single misconfigured cloud storage bucket or an unprotected account can expose sensitive data. In Malaysia, compliance frameworks such as the Personal Data Protection Act (PDPA) require companies to safeguard customer information. Failure to do so risks penalties and reputational loss.
Cloud security directly affects business continuity, customer confidence, and the ability to scale safely. That is why investing in stronger cloud practices has become a board-level concern for enterprises.
Practice 1: Data Encryption
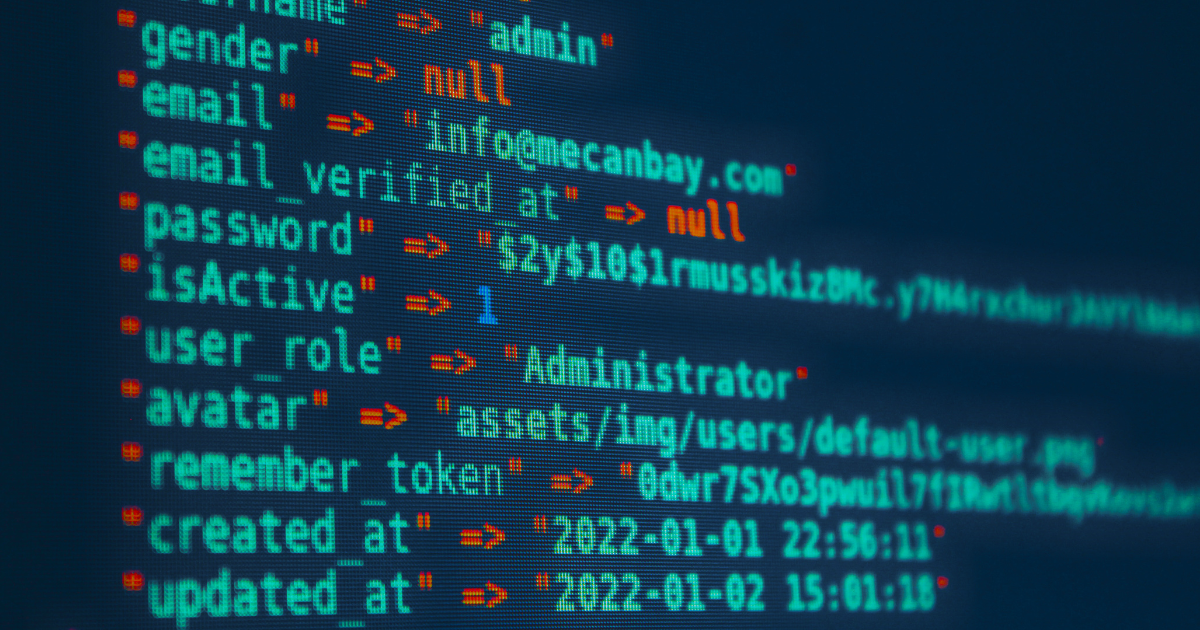
Data encryption is one of the most effective ways to secure information in the cloud. It encrypts and decrypts files both at rest (when stored) and in transit (when transferred between users or applications). Only authorized users with the correct keys can unlock the data.
For example, a local finance company in Kuala Lumpur may encrypt its daily transaction backups stored in the cloud. This ensures that even if attackers intercept the data, they cannot read or misuse it.
Encryption also helps organizations demonstrate compliance with PDPA and international standards like ISO 27001. In practice, this means reduced risk of fines and stronger customer trust.
Practice 2: Multi-Factor Authentication
Multi-Factor Authentication (MFA) adds an extra layer of defense by requiring users to authenticate and verify their identity with more than just a password. This usually combines something the user knows (a password), something they have (a mobile device or token), or something they are (biometric verification).
MFA reduces the risk of unauthorized access caused by stolen or weak passwords. A retail chain, for example, may require staff to use both their password and a one-time code sent to their phone when logging in to the point-of-sale system. Even if attackers manage to steal the password, they cannot enter without the second factor.
MFA is simple to implement across common platforms like Microsoft 365, Google Workspace, and cloud management consoles. By making MFA a standard requirement, companies strengthen user authentication and reduce account takeover risks.
Practice 3: Firewalls Protection
A firewall acts as the first line of defense for cloud-based applications. It blocks, filters, and logs traffic moving between internal systems and the internet. This ensures that only trusted requests reach critical business applications.
Modern firewalls have evolved into cloud-native firewalls or Web Application Firewalls (WAFs), which protect workloads running in AWS, Azure, or Alibaba Cloud. For example, a hospitality business managing an online booking system can use a WAF to stop malicious traffic and filter out potential SQL injection attempts.
Callnet partners with providers such as Cisco and Sangfor to help businesses deploy firewalls that not only block threats but also generate real-time logs for monitoring. This gives IT teams visibility into traffic patterns and potential attacks.
Practice 4: Endpoint Protection
Endpoints, such as laptops, smartphones, and tablets, are often the weakest link in cloud security. Endpoint protection solutions detect, isolate, and protect devices from malware, ransomware, and phishing attempts.
For companies with remote staff, endpoint protection is essential. Consider a logistics firm where employees use mobile devices to update shipment status via a cloud app. Without endpoint security, one infected device could compromise the entire platform. With endpoint protection in place, suspicious activity is identified and isolated before it spreads.
Endpoint protection is more effective when combined with centralized monitoring and automatic updates. This ensures every device connected to cloud services remains secure, regardless of where employees are working.
Practice 5: Backup and Recovery
Cloud backup and recovery solutions store, encrypt, and restore business data in case of loss. Combined with disaster recovery plans, they restore and fail-over systems during outages to keep operations running.
Say you are running a retail business across different states in West Malaysia, you may back up your point-of-sale data daily to the cloud. If a ransomware attack locks the primary system, your team can quickly restore from a clean backup. This prevents long downtime and avoids costly business disruptions.
Regular testing of recovery processes is just as important as creating backups. Businesses that only store data without testing restore procedures risk finding gaps when a real incident happens.
Practice 6: Continuous Monitoring
Continuous monitoring tools monitor, alert, and diagnose security events in real time. They help businesses detect abnormal patterns such as unusual login attempts, traffic spikes, or unauthorized access.
For e-commerce platforms, early detection is critical. A sudden flood of traffic could signal a Distributed Denial of Service (DDoS) attack. With monitoring tools like PRTG, SolarWinds, or Splunk, IT teams can receive alerts and take action before the attack disrupts customers.
Continuous monitoring also supports compliance reporting by generating logs that prove businesses are actively watching for threats. This provides assurance to both regulators and customers.
Practice 7: Compliance Management
Compliance frameworks audit, enforce, and verify how businesses manage cloud data. In Malaysia, the Personal Data Protection Act (PDPA) applies to any company that processes customer information. Global standards like ISO 27001 and PCI DSS are also common requirements in industries such as finance and retail.
For businesses, compliance is more than just paperwork. A solid policy defines who can access what data, how long records are retained, and what controls are in place to prevent misuse. By aligning cloud practices with compliance requirements, companies reduce legal risks while demonstrating accountability.
SMEs can start by performing simple audits: checking access permissions, verifying encryption settings, and ensuring cloud providers meet regional compliance requirements.
Practice 8: Employees Training
Technology alone cannot secure the cloud. Human (your employees!) an equally important role in securing your cloud environment. Regular training helps staff recognize phishing emails, avoid unsafe file sharing, and report suspicious behavior.
For example, a hotel chain may provide cloud access to its front-desk staff for guest management. With proper training, staff can identify fraudulent emails disguised as customer requests, reducing the chance of a breach.
Security awareness programs should be practical, ongoing, and tailored to different departments. When employees understand how their actions affect cloud security, the entire business becomes more resilient.
What Should Businesses Do Next to Strengthen Cloud Security?
Cloud security is not a one-time effort — it requires continuous attention. By applying these eight practices, you can protect sensitive data, maintain compliance, and ensure safer operations in the cloud.
Callnet Solution helps Malaysian enterprises protect, monitor, and recover their cloud environments through tailored IT solutions and partnerships with global technology providers.
Discover our cloud solutions in Malaysia or request a free consultation to learn how we can support your business growth securely.